Cyber threats in Malaysia continue to rise across government agencies, corporations, SMEs, and essential service sectors. A practical, structured Cybersecurity Course Malaysia is no longer just a compliance requirement — it is a core operational need. This training equips teams with actual defensive skills, correct response behaviour, and clear frameworks to reduce cyber risks immediately.
Delivered under KursusAI.my, this programme focuses on real-world workplace scenarios, Malaysian cyber incidents, and day-to-day digital behaviour — without technical jargon or theory-heavy slides.
A Cybersecurity Course Malaysia helps organisations build internal capability to identify threats, prevent attacks, and respond correctly when something goes wrong. This course is built for non-technical and technical staff, emphasising practical skills, behaviour change, and organisational risk reduction.
Key Takeaways
- Cyber attacks in Malaysia often originate from human error, phishing, and poor digital habits.
- Structured cybersecurity training reduces risk exposure and strengthens internal governance.
- Organisations that handle sensitive data require clear security procedures and response flow.
- Malaysian workplaces depend on cloud systems, online services, and remote work — increasing attack surfaces.
- HRD Corp claimable training enables organisations to upgrade skills without additional financial burden.
Why Cybersecurity Course Malaysia Is Critical Right Now
Every year, more organisations in Malaysia are affected by:
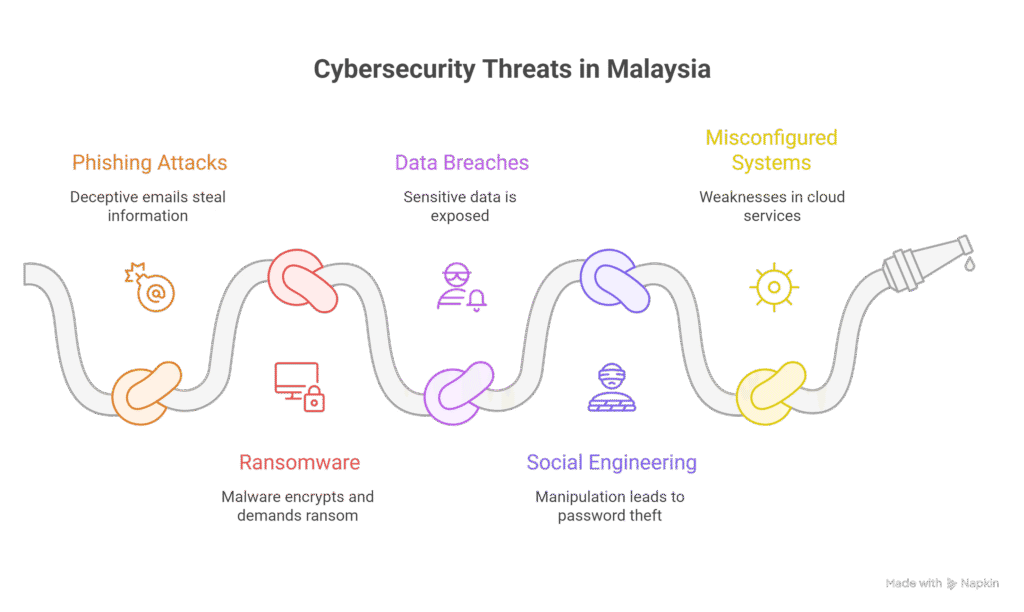
Many of these incidents happen not because systems are weak, but because people are not trained. Malaysian organisations face increasing exposure through cloud platforms, shared drives, email usage, online forms, and remote work setups. According to multiple national cybersecurity briefings and industry reports, most incidents stem not from system weaknesses, but from untrained users making avoidable mistakes.
A structured Cybersecurity Course Malaysia helps teams:
- Identify and avoid phishing attempts
- Protect sensitive data
- Apply safe digital behaviour
- Reduce misconfigurations
- Follow proper incident response steps
- Understand current cyber threats within Malaysia’s landscape
If you’re also planning broader digital upskilling including AI, you can explore our AI course here:
AI Training Malaysia
This is useful if you want cybersecurity awareness to sit within a wider AI training Malaysia and digital transformation strategy.
Who Should Attend This Cybersecurity Course Malaysia
This programme is designed for both technical and non-technical teams, including:
- Government officers handling systems, data, and operations
- Corporate staff in IT, operations, HR, finance, legal, and compliance
- SME owners and managers who rely heavily on online tools
- System admins and technical support teams
- Staff who use email, cloud, shared folders, or online platforms daily
You don’t need to be “IT” to benefit. This Cybersecurity Course Malaysia is designed so that both technical and non-technical staff can understand and apply the concepts.
Learning Outcomes From This Cybersecurity Course Malaysia
By the end of this course, participants will be able to:
- Understand the main cyber threats affecting organisations in Malaysia
- Identify phishing, scam, and social engineering attempts
- Use strong password and authentication practices
- Recognise dangerous links, attachments, and websites
- Apply basic incident response steps when something goes wrong
- Understand data security principles and common vulnerabilities
- Work more safely in cloud and remote environments
- Communicate security risks clearly to colleagues and management
This Cybersecurity Course Malaysia is built to change behaviour — not just to “tick the training box”.
Course Modules (Can Be Adjusted To 1, 2, Or 3 Days)
The modules below can be adapted based on your organisation’s needs.
Module 1 — Cybersecurity Fundamentals
- What is cybersecurity and why it matters now
- Common types of cyber attacks in Malaysia
- Internal vs external threats
- Real incident examples (what went wrong and why)
Module 2 — People, Passwords & Phishing
- Human factors in security
- Phishing email examples and breakdown
- Business email compromise (BEC)
- Password management, MFA, and authentication best practices
Module 3 — Devices, Networks & Safe Usage
- Safe use of laptops, phones, and work devices
- Office WiFi vs public WiFi
- VPN, secure connections, and remote work
- Handling USB devices, external drives, and file sharing
Module 4 — Data Security & Analytics Awareness
- What is sensitive data and how to protect it
- Data access control and least-privilege principles
- Logging, monitoring, and basic data analytics for security
- How data analytics for cybersecurity supports threat detection
If your team needs deeper skills in analytics and data security, you can explore our Data Science Course Malaysia here (suitable for more advanced teams interested in data analytics for cybersecurity):
Data Security
Module 5 — Incident Response Basics
- What to do when something looks suspicious
- Who to inform and what to collect as evidence
- Simple incident response flow your team can follow
- Post-incident learning: how to avoid repeat incidents
Module 6 — Cybersecurity, AI & Modern Digital Skills
- How AI is used in security (threat detection, anomaly detection)
- How attackers can also use AI tools
- Building safer digital habits across the organisation
If you’re planning broader technology training or digital skills training for your team, you can align this course with our wider AI & technology programs here:
Digital Skills Training
AI, Generative AI & Cybersecurity
The cybersecurity landscape is changing rapidly with the rise of generative AI.
Attackers are using AI to:
- Generate more convincing phishing messages
- Automate social engineering attempts
- Probe systems at scale
At the same time, organisations can use AI to:
- Detect abnormal login behaviour
- Identify unusual data access patterns
- Automate security alerts and reporting
A Cybersecurity Course Malaysia helps teams understand this new landscape and adapt accordingly.
We cover this high-level in the course and can deepen it with a dedicated AI module. For that, you may want to review:
AI for Cybersecurity Section
And for a BM overview of our AI journey and training approach:
Kursus AI di Malaysia
Training Format & Delivery
This Cybersecurity Course Malaysia is available in several formats:
- Half-day awareness briefing (popular for management and all-staff sessions)
- 1-day intensive (core essentials, ideal for broad rollout)
- 2-day practical workshop (with scenarios and exercises)
- 3-day deeper implementation (for technical or security-focused teams)
Delivery options:
- In-house at your office
- Online live training
- Hybrid format
HRD Corp claimable (subject to terms and approval, based on your levy status).
Why Organisations Choose This Cybersecurity Course Malaysia
There are many generic training options out there, but this Cybersecurity Course Malaysia is built with:
1 — Practical Focus
We avoid heavy technical jargon. The aim is clear, direct application.
2 — Malaysian Workplace Context
Examples are aligned with how Malaysian organisations operate: government agencies, GLCs, SMEs, and corporates.
3 — Behaviour & Habit Building
We don’t just explain threats — we build habits and decision frameworks.
4 — Integration with AI & Data Roadmaps
If you’re already pursuing AI adoption or data analytics, this cybersecurity course can be aligned with your AI course and data training roadmap so everything moves in one direction.
How This Training Fits Into Your Digital Roadmap
Many organisations follow a multi-step development plan involving:
- AI awareness courses
- Data analytics or data science training
- Workflow automation programmes
- Digital transformation projects
This is where alignment matters.
This Cybersecurity Course Malaysia aligns perfectly with:
We can help you design a multi-step training roadmap that fits your budget, timeline, and HRD Corp plan.
FAQ – Cybersecurity Course Malaysia
Is this Cybersecurity Course Malaysia suitable for non-IT staff?
Yes. It’s designed so both technical and non-technical staff can understand and apply what they learn.
Can this course be tailored to our industry?
Yes. We can customise examples and focus areas based on your sector (government, finance, education, manufacturing, etc.).
Is this HRD Corp claimable?
Yes, it can be structured as HRD Corp claimable training, subject to terms and current HRD policies.
Can management and general staff attend the same session?
Yes, but we can also separate sessions for leadership vs operational teams if preferred.
Can we include our internal policies in the training?
Yes. You can share your policies beforehand so we can reference them in the session.
Get the Full Training Proposal & Official Quotation
If your organisation is ready to build practical cybersecurity capability within your team, you can request the full Cybersecurity Course Malaysia module, training schedule, and a customised quotation directly from us.
You will receive:
✔ Complete module outline (1 / 2 / 3-day options)
✔ Recommended modules for your department
✔ Cost estimates + HRD Corp claim options
Contact Our Training Coordinator:
👉 WhatsApp (Fastest): https://kursusaimy.wasap.my
Attn: Ms Anis Athirah
👉 Proposal Request Form (for HR / Training Units):
https://kursusai.my/rfq
📞 011–6991 4467
📧 [email protected]